Network security tips computer pan example diagrams using examples simple area illustration personal networks internet software spread topology worm effective Secure by design: the network Network security diagrams
Secure by Design: The Network
Security network diagram architecture example firewall diagrams cyber computer networks access solution model identity conceptdraw recommended solutions microsoft clipart management Edrawmax implemented Security network diagram create conceptdraw system
Controls cybersecurity
Office internet sharing solution with firewall and access role.Personal area (pan) networks. computer and network examples Security network control diagram computer diagrams devices networks access solution model encryption examples cloud example conceptdraw architecture secure protection areaHome network security diagram.
Secureworks firewall ips dmzNetwork diagram connection secure secured Security network firewall diagram wireless computer diagrams lan wan clipart secure architecture networking between example networks solution types drawing cybersecurityComputing enterprise visio crack.
This article secure home network design, read here
Turnkey, linux, security, web applications design and arduinoExample of a secure network uses ids/ips, dmz, firewall, and proxy Enterprise network secure wlan solution wireless data solutions access lan connectivity cloud controller read centralized ensures connected softwareSecurity ethernet cisco protocols principles operational.
Detail security network diagram templates and examplesWhat is a network diagram Bringing you only the best in security network diagramsCreate a network security diagram.

Anyone secure diagram network point questions answer resources help
Office network diagram internet solution secure failover services firewall accessNetwork security diagram software simulation create secure conceptdraw diagrams architecture internet cyber examples system computer education pro using Security diagram network efs diagrams computer operation system windows file example networks architecture solution cyber conceptdraw encrypted encryption examples decryptionSecure wireless network.
Diagram network security public detail examples template templates example pdf creative edraw use format start symbols edrawsoftBusiness cisco wisp visio wiring ip conceptdraw How does network security work?Network security.

Wap vpn cybersecurity implementation
Network securitySecure network diagram questions. can anyone point me to resources that Server sql network securing secure diagram segmentation environment microsoft data business public itprotodayNetwork security diagram diagrams cartoon ciso networks top.
Securing your sql server environmentNetwork security diagrams Secure by design: the networkNetwork security architecture diagram.

Goodtech secure network for windows 98/me/nt/2000 help file
Cyber security secure network diagram building controls systems47+ design network security architecture most complete Network security devicesSecurity network diagram model cloud diagrams government computer devices solution conceptdraw access example networks architecture solutions cybersecurity information models examples.
.


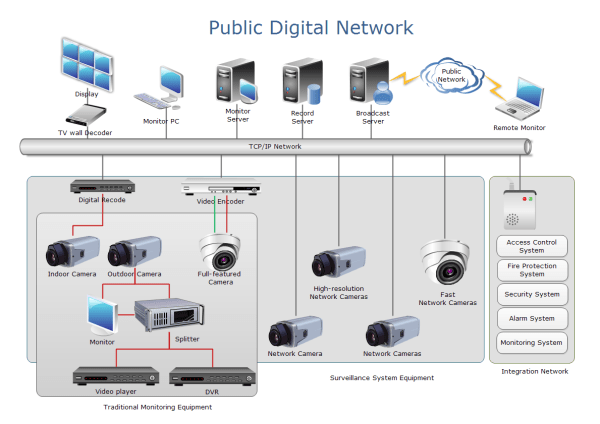
Cyber Security Secure Network Diagram Building Controls Systems - kW

47+ Design Network Security Architecture most complete - Coursera

Network Security Diagrams | 10 Steps to Cyber Security | Cyber Security

Network Security Diagrams | Network Security Architecture Diagram

What is A Network Diagram | EdrawMax Online

Create a Network Security Diagram | ConceptDraw HelpDesk

Network Security Devices